Discover what ION can do for you
About Reval
Companies are not static. Neither are their treasury departments. New markets or acquisitions mean increasing complexities, like new regulatory requirements, more banks, more currencies, asset classes, and risk. With Reval, treasuries can easily adapt to their changing environments, managing treasury and risk effectively with an innovative, highly scalable SaaS (Software as a Service) solution.
Why Reval
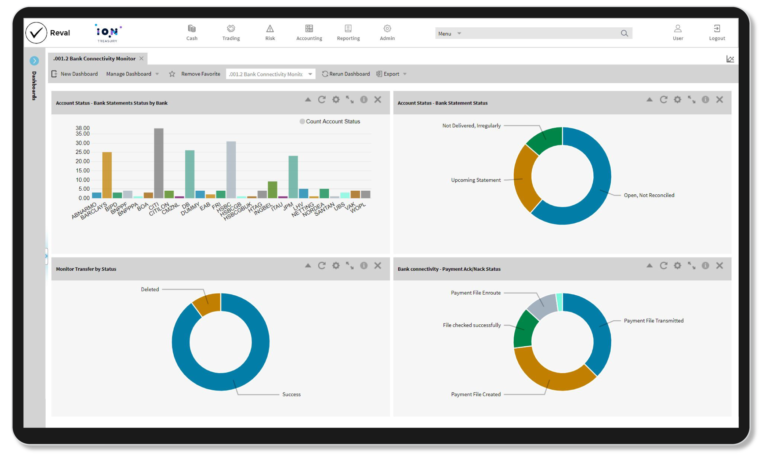
Reval helps companies better manage cash, liquidity, financial risk, and hedge accounting. Its capabilities are comprehensive and integrated, leveraging the power of its partner community to deliver a seamless user experience. Additionally, Reval makes it simple to comply with increasingly complex regulations.
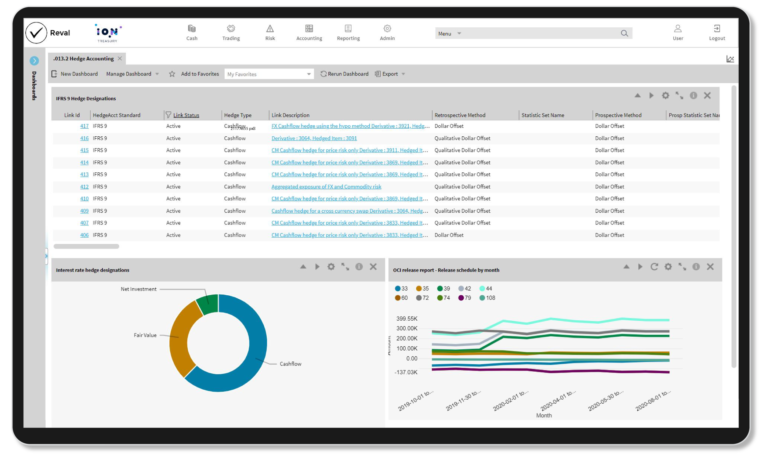
Execute hedge accounting strategies with market-leading tools.
Manage FX, investments, debt, credit facilities, intercompany loans, and deals.
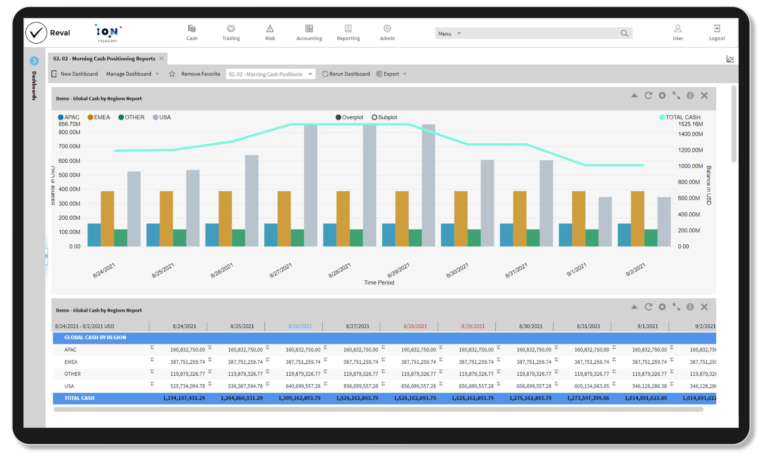
Streamline daily cash management processes.
Automate internal banking services, like POBO, COBO, FX requests, and working capital.
Mitigate credit, market, and liquidity risks.
Grow with a highly scalable SaaS delivery model.
Key features
Hedge accounting expertise
Benefit from over 20 years of market leadership for hedge accounting and valuations.
Access to Hedge Accounting Technical Taskforce (HATT) expertise.
Reval clients are consistent early adopters of new standards and regulations.
SaaS offering
Automatically receive major upgrades twice a year along with superior market data.
All in an easy-to-use, low IT impact, cloud environment.
Stay updated with new functional standards, market innovations, compliance, and accounting requirements.
STP community and market data
Connectivity to FXall, 360T, Misys, SAP, Oracle, ICD, Goldman Sachs Mosaic, and more.
Integrated market data is also provided as part of the base package.
Enhance your treasury software with optional value-added solutions
At ION Treasury, we innovate at scale. We build new innovative tools and roll them out to our entire product portfolio, offering cutting-edge technology to all ION Treasury customers. Our latest innovations include solutions for bank account management with bank fee analysis, money market funds, machine learning, and mobile treasury.
IBAM
Web-based bank account management with bank fee analysis capabilities enabling users to maintain a centralized, accurate inventory of all bank accounts and bank documentation.
Machine learning
Enhanced capabilities powered by artificial intelligence and machine learning. Fast, accurate algorithms optimize the potential of your data to deliver new insights.
Money market funds
A seamless money market funds experience enabling full automation of the trade lifecycle. Real-time consolidated investment and cash reporting, and access to a rich set of money market fund data and analytics.
Treasury Anywhere
Access information from your ION treasury management system anywhere using any mobile device, tablet, laptop, or PC.
Frequently Asked Questions
What does a Reval implementation project look like?
Reval typically takes three to six months to implement, depending on the size and scope of the project.
What deployment options are available for Reval?
Reval is a multi-tenant Software as a Service (SaaS) solution.
With what other platforms does Reval integrate?
Reval supports connectivity to FXall, 360T, Misys, SAP, Oracle, ICD, Goldman Sachs Mosaic, and more.
For which type of companies is Reval best suited?
Reval is built for global corporations looking to better manage cash, liquidity, and risk, along with accounting for and reporting on complex financial instruments and hedging activities.
Latest Treasury awards
RiskTech100 2024
IDC MarketScape 2023 Vendor Assessment
Stevie Awards 2023
Central Banking’s Awards 2023
Related products
City Financials
A pre-configured treasury and risk management solution that provides efficiency and strong controls using standard treasury practices.
IT2
A configurable treasury and risk management solution that offers a superior visual user experience and an integrated workflow framework.
Openlink
A comprehensive enterprise treasury and risk management solution for large commodity-intensive organizations needing extensive asset class coverage.
Wallstreet Suite
An enterprise treasury and risk management solution designed for the unique needs of the world’s largest, most complex organizations.
